Is Infotech Lifafa Real or Fake?
Is Infotech Lifafa Real or Fake Let’s cut to the chase — you’ve probably come across Infotech Lifafa online and…
Riding the Surge in Online Shopping Trends
Riding the Surge Online shopping, long a convenient alternative to traditional retail, has solidified its place as the leading channel…
The First Aircraft of its Kind in the World is Fully Electric
Introduction It is the first time that the world’s first electric-powered commercial aircraft has launched. On its first test flight…
Fashnear Technologies Pvt Ltd – Contact Details and Insights
About Fashnear Technologies Pvt Ltd Fashnear Technologies Pvt Ltd is a private Indian company incorporated on 12/13/2014 with its registered…
6 Phone Apps to Organize Your Life
Introduction There are thousands of applications, some of which claim to help us organize our lives like calendars, and finding…
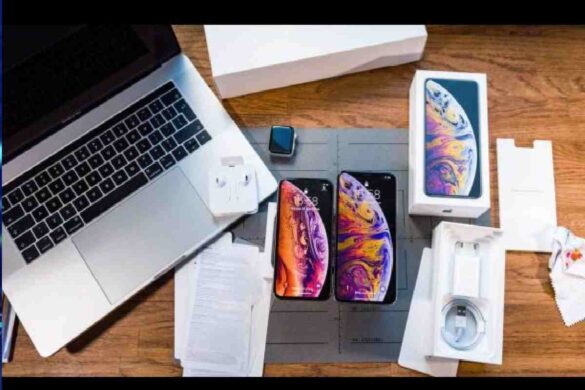
iPhone XS Max Ashes of the Singularity Wallpaper – Complete Guide
Introduction Sure, here is an iPhone XS Max Ashes of the Singularity wallpaper: This wallpaper features a stunning image of…
Launching a New wi-fi Network Services
Introduction The Wi-fi network has moved to the sixth generation, which does not reflect its age (much older). But it…
Fastest Supercomputer – Introduction, Supercomputer and More
Introduction In the opinion of many of us. The supercomputer seems fast enough if it can play lego lord of…